KALKI.IO Remote Device Maintenance provide a secure remote device access and management service for your equipment and assets
Kalki.IO Remote Device Maintenance is a secure, cloud-based service that allows you to establish secure communication tunnel with the devices or assets anywhere in the world. The secured tunnel created using Kalki.io remote access service enables you to is securely access, maintain and manage the field devices and assets 24/7 without been near to the device.
Ease of Deployment & Management : Web based console equip administrators to easily configure access / monitor and control the sessions
Zero trust Access: Controlled exposure of devices and applications does not expose entire network limiting lateral attacks
Scalable & Flexible: support millions of both managed or unmanaged resources, legacy devices and software applications
VPN Free: No exposed public gateways, reduces DDoS and malware attack

KALKI.IO Remote Device Access service provides remote configuration and management access of field devices by securely extending the connectivity between device’s programming port and engineering tool over a public/private network. Remote device access service also can be used to acquire data from a device over a wide number of utility, industry telemetry & IoT protocols supported.

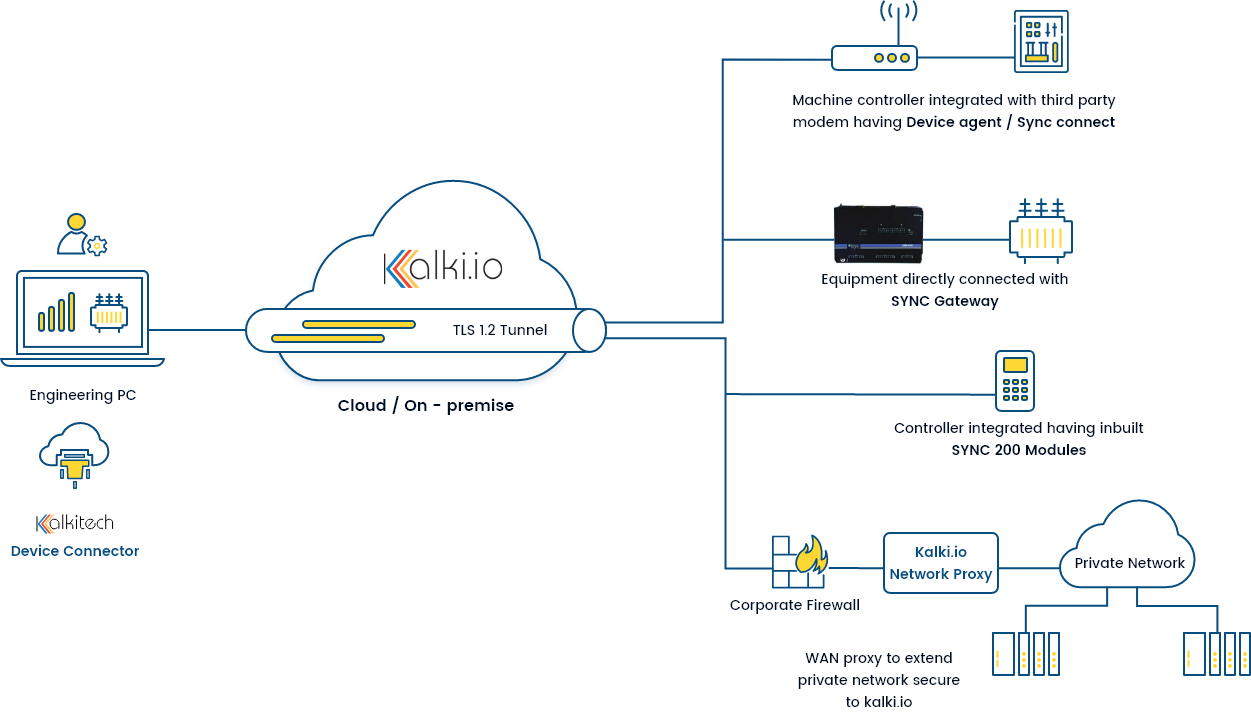
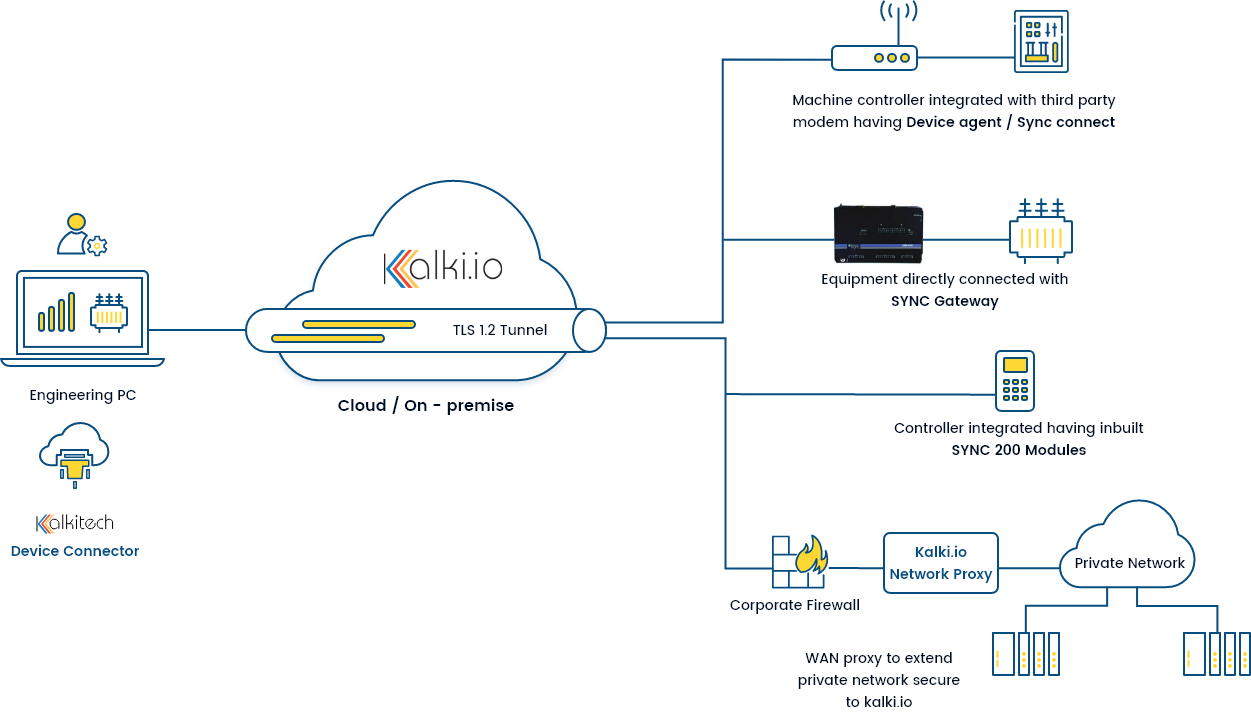
Provides an outbound connection from the industrial or utility network with Kalki.io provides a secure TLS tunnel with resources in the field resources. Kalki.io Edge (KIOE) supporting commonly used utility and industry protocols like Modbus, IEC-60870, DNP3.0, etc also can be used as a proxy for secure connecting. KIOE runs in any standard Linux OS based hardware/Virtual Machines/Containers. Validated in many commercial off the shelf hardware

Edge Proxy provides a standard methodology for establishing a secure connectivity end to end tunnel from resource constrained devices like modems or devices communication modules to KALKI.IO

SYNC series of gateways /module are ruggedized hardware for communicating with devices installed in substations or power utility’s T&D network. These devices comes with pre-installed with Kalki.io Edge/proxy software.
Interested in knowing more about the product
Request for demoKalkitech’s cloud-based remote maintenance system provides a zero-trust secure remote access service for your devices and equipment.
Kalki.io service helps the equipment manufacturers to improve reliability by pro-active maintenance and increasing the asset productivity by reducing downtime; helps asset owners to reduce the risk of network and data breaches; O&M service providers to reduce O&M costs and engineering complexity, protect assets & equipment by taking on-time action. The main differentiating factor of the Kalki.io remote device maintenance access solution is its ease of use by reducing system setup complexity and improved security by zero trust access control technology, which makes it ideal for the industries to connect field devices, software, and services.
An increase in the number of connected devices and software because of rapid improvement in sensor and connectivity technology increases the demand for secure remote control and management of these devices. Kalki.io remote device maintenance access solution makes it easy to securely organize, monitor, and remotely manage your remote assets and resources at scale. Kalki.io service provides secure connectivity between the device’s programming port and its engineering tool over a private/ public network. Over the past few years, the maintenance strategy of asset owners is changing from Reactive → Planned → Proactive → Predictive maintenance. The real-time collection of assets, health, and operational data are important to enabling this migration.
Kalkitech deploys a centralized secure remote access management system for the complete management and monitoring of devices/equipment in the asset-located fields. It is more beneficial than VPN based solution and has a device as well as user-level access control. Users can make use of this technology framework to establish secure connectivity with the distributed assets and helps users to reduce engineering time, costs, and resources.
Kalki.io platform also facilitates remote monitoring of resources such as field devices or software for effective monitoring of the health and operational data.
Kalki.io Remote device maintenance access works directly with the field resources or using third-party edge hardware or field gateways. With an inside-out connectivity model, it provides unlimited connections as there is no dependency on the IP like traditional VPN technology. Besides improving the reliability by pro-active maintenance, this secure remote access management solution increases asset productivity by decreasing downtime. It also has UI to monitor the status on a remote PC and provides better performance on the lossy network. Kalki remote device pack streamlines operations, thereby improving the performance and maintenance efficiency of industries.
